Here Is How One Email From Your Boss Could End With a $28,239 Loss
The accounting scams are multiplying by the day. A new scam targeting people working in the accounting industry is making its rounds these days. If you know any financial controllers, managers, auditors, or simple accountants, please share this information with them. The scary and easy-to-fall-for scam was exposed to us by Suzana S., Financial Controller at EnReach Hot Tap Services, a Canadian field engineering services.
You could become a victim of this scam regardless of your city, province, state, or country. The trick is the same, but it's adjusted according to the company. Here is how the scam works.
Scam Detectors Most Trusted Websites in Online Security
- Guard.io (100): Surf the web safely. Clean up your browser, remove maliscious extensions and check for privacy violations.
- Incogni.com (100): Delete your personal data from the internet and protect against scams and identity theft.
- ExpressVPN (100) Stay secure and anonymous online - Best VPN Out There
As many accountants work from home, whether there is a pandemic or not, so does Suzana. She received an email during business hours. It from her boss and owner of EnReach, David – or so she initially thought. The name of the sender was her boss's full name.
The email subject was “Management Consultancy Services,” and the message was this:
“Hi, Suzana,
Can you initiate a transfer that goes out today?
If you could expedite this, notify me when you are set to proceed so I can forward an attachment of the payment instructions.
Thanks,
David”
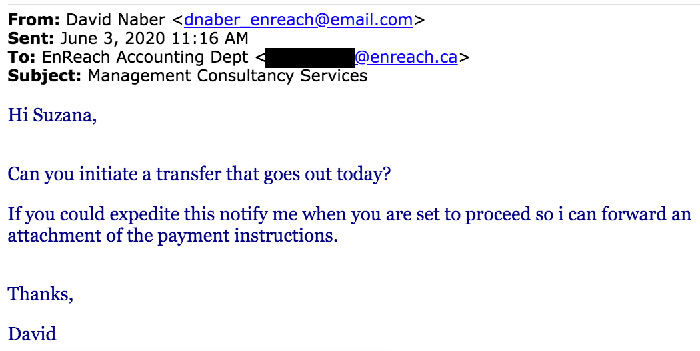
As she receives similar emails as a financial controller, Suzana didn't initially have any major doubts. The email address of “David” contained the word “EnReach,” too, so at a glance, any discrepancies were not noticeable, although there were a couple of them that would give away the scam (we'll talk about them later). However, Suzana replied with a confirmation, but she asked for more info.
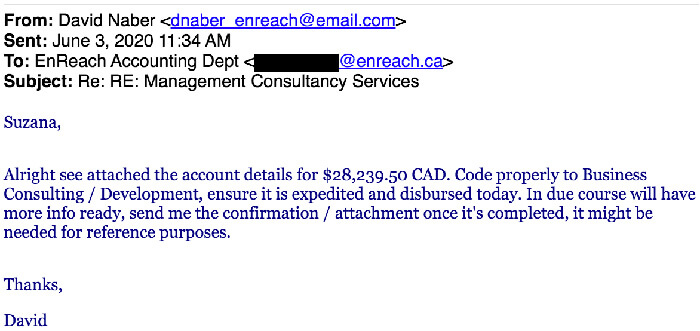
The fake David responded with a message in which he used familiar terms that accountants use. Here is what he said:
“Suzana,
Alright, see attached the account details for $28,239.50. Code properly to Business Consulting/Development, ensure it is expedited and disbursed today. In due course will have more info ready, send me the confirmation/attachment once it's completed, it might be needed for reference purposes.
Thanks,
David”
Phrases such as “code properly” or “expedited and disbursed today” are barely used by regular people, so no red flags were raised either. The attachment contained the bank details of a certain Lauren Scott in Toronto. “David” referenced the transaction as “Management Consultancy Services” to Scott.
Here is a screenshot of the email:
Not wanting to disturb the owner of her company with a call to inquire about the veracity of the email, Suzana placed the $28,239.50 into CMO (Cash Management Online), a platform used before the final transfer. These CMO funds require the signature of one of her superiors in order to get the money out to the recipient. Luckily, before it was too late, the transaction was stopped, and money didn't go to Lauren Scott.
The story is similar to the infamous loss of $11M incurred by the Grant MacEwan University when a scammer started a correspondence with the Accounting Department claiming to be from Clark Builders. This well-known construction company had most of the University's contracts. Using the right verbiage and impersonating the right people who had the authority to give the green light, the criminal got the financial controller at MacEwan to wire over $11 million into accounts that transferred the money to Hong Kong. Luckily, most of the funds were recovered after a couple of years of investigations, but the morale is that these days everyone could be anyone on the internet.
There are a few questions that someone could ask if they look at the case:
1. How did the scammers know who to contact exactly within the company?
2. How did the scammers know what to say precisely to avoid signaling a scam?
3. What would give away the fraud? How would an accountant detect criminal activity?
Let's look at the answers. Some people may say that the scammers may have known some internal logistical secrets – hence the specific language and the laser-targeted person to approach – however, it may not be the case at all. Let us explain.
1. How Did The Scammers Know Who To Contact?
Social media is great for communication, but in many cases, it is the easiest way to find information about a victim. In this case, the crook found out who the financial controller is at EnReach Hot Tap Services. LinkedIn is the place to provide all the necessary information for that. Not only the platform features your title with your company but showcases details and things you are responsible for (yup, you wrote those down yourself).
It is even easier to find the owner or the manager of a company.
2. How Did The Scammers Know Precisely What To Say?
How did the criminal address such an important transaction using words that the internal staff does? Sure, it could have been someone who used to work there or a former niche employee, but it could be much simpler. Criminals hack emails, read a regular correspondence between you and your superiors, and create an email chain that features a pattern you are used to. This might have been the case in both Suzana's and MacEwan's approach.
Are you wondering how easy it is to hack someone's email? Easy. Here is how to hack an email address with a mobile phone.
3. What Are Some Red Flags When Receiving an Email?
If we look at Suzana's first email, there are a couple of things that stick out. First, the email address that “David” used was of a personal email. Although it contained the name of the company, EnReach ([email protected]), it did not have it under the domain name. It may go unnoticed since the peripheral vision senses the name of the company.
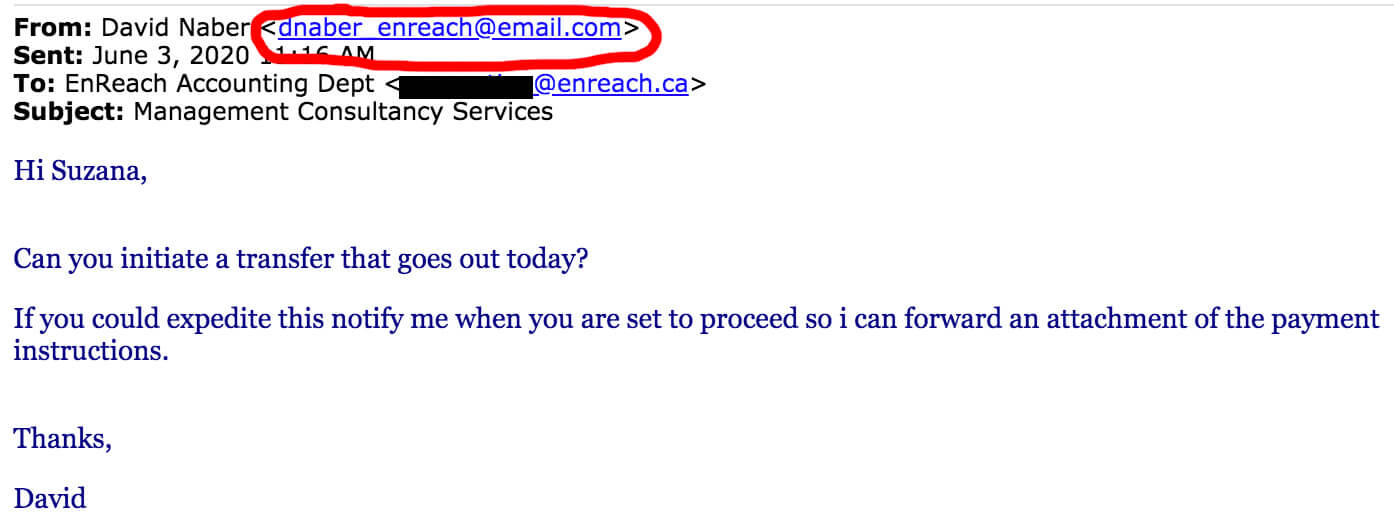
Second, which somehow relates to the first, when owners or managers of big companies send an internal email, that message has a signature which 100% of the time has the logo of the organization, phone number, or email. At least, at respectable companies. It didn't happen with this email.
The urgency of the situation represents the third red flag. The fake David asked the company's financial controller to initiate the transaction “today.” Contact your superiors if you receive such a rushed request.
The Accounting Scam: How To Report
Warn your family and friends about this accounting scam by sharing the article on social media using the buttons provided. You can also officially report the scammers to the Federal Trade Commission using the link below:
How To Prevent Identity Theft and More
If you want to be the first to find out the most notorious scams every week, feel free to subscribe to the Scam Detector newsletter here. You'll receive periodic emails – we promise not to spam. Last but not least, use the Comments section below to expose other scammers.
Verify a website below
Are you just about to make a purchase online? See if the website is legit with our validator:
vldtr®


TOP 4 MUST-WATCH FRAUD PREVENTION VIDEOS
1. Top 5 Amazon Scams in 2024 2. Top 5 PayPal Scams in 2024 3. How To Spot a Scam Email in 2024
- Latest Posts by Selma Hrynchuk
-
Compromised Credit Card Scam
- -
Fake Google Chrome Update
- -
Facebook Privacy Notice Hoax
- All Posts













