Zero Day Vulnerability Email Scam: How It Works
Also known as the Sextortion approach, the Zero Day Vulnerability Email Scam is a notification meant to get all your personal data by using a scare tactic. You might receive this email very soon, as it’s making its rounds on the Internet and it’s spreading like fire. Let’s take a look at this message and check out the best practices when it comes to email scams.
Did you receive an email like the one below? Even if you did not, it’s worth a quick read in case you will get it – because it’s about external control over your computer. The grammar mistakes are also included:
Scam Detectors Most Trusted Websites in Online Security
- Guard.io (100): Protect your digital world on any device – Guardio stops scams and phishing in their tracks.
- Incogni.com (100): Delete your personal data from the internet and protect against scams and identity theft.
- ExpressVPN (100) Stay secure and anonymous online - Best VPN Out There
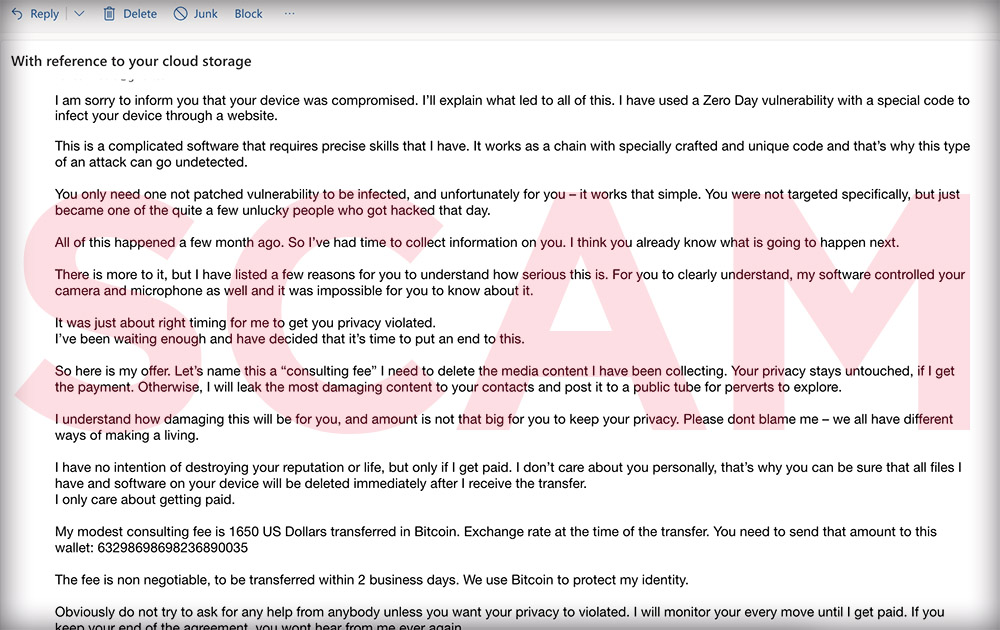
“Subject: With reference to your cloud storage”
“I am sorry to inform you that your device was compromised. I’ll explain what led to all of this. I have used a Zero Day vulnerability with a special code to infect your device through a website.”
“This is a complicated software that requires precise skills that I have. It works as a chain with specially crafted and unique code and that’s why this type of an attack can go undetected. You only need one not patched vulnerability to be infected, and unfortunately for you – it works that simple.”
“You were not targeted specifically, but just became one of the quite a few unlucky people who got hacked that day. All of this happened a few month ago. So I’ve had time to collect information on you.”
“I think you already know what is going to happen next. There is more to it, but I have listed a few reasons for you to understand how serious this is. For you to clearly understand, my Zero Day vulnerability software controlled your camera and microphone as well and it was impossible for you to know about it. It was just about right timing for me to get you privacy violated.”
Extortion Tactic 101
The crook continues:
“I’ve been waiting enough and have decided that it’s time to put an end to this. So here is my offer. Let’s name this a “consulting fee” I need to delete the media content I have been collecting. Your privacy stays untouched, if I get the payment. Otherwise, I will leak the most damaging content to your contacts and post it to a public tube for perverts to explore.”
“I understand how damaging this will be for you, and amount is not that big for you to keep your privacy. Please dont blame me – we all have different ways of making a living. I have no intention of destroying your reputation or life, but only if I get paid. I don’t care about you personally, that’s why you can be sure that all files I have and software on your device will be deleted immediately after I receive the transfer. So, I only care about getting paid.”

Here is more:
“My modest consulting fee is 1650 US Dollars transferred in Bitcoin. Exchange rate at the time of the transfer. You need to send that amount to this wallet: [NUMBER]. The fee is non negotiable, to be transferred within 2 business days. We use Bitcoin to protect my identity.”
“Obviously do not try to ask for any help from anybody unless you want your privacy to violated. I will monitor your every move until I get paid. If you keep your end of the agreement, you wont hear from me ever again.”
Take care.”
Good News: You Were Not Hacked
You were not hacked – at least not by this guy – so no worries. Criminals send this email to millions of people at once by using addresses purchased from third parties or even collected by them over time. It’s that easy. So, just delete the message.
The Zero Day Vulnerability Email Scam could have a different variation. Watch the clip below to see it described in video format.
Zero Day Vulnerability Email: How To Report a Scammer
Warn your family and online friends now about the Zero Day Vulnerability Email by sharing this article on your social media platforms. You can also officially report the criminals or any other suspicious activity to the Federal Trade Commission (FTC) using the link below:
How To Prevent Identity Theft and More
If you want to be the first to find out prevalent scams on a weekly basis, then subscribe here to the Scam Detector newsletter. You’ll receive periodic emails from our fraud prevention experts – and we promise not to spam. Meanwhile, educate yourself with some other must-read articles listed right under this paragraph, so that you can protect yourself. Last but not least, feel free use the comments section below to expose other crooks. Share your experience and help others.
Here are some great reads for the end:
Did You Receive an Email From Your Own Email Address?

TOP MUST-WATCH FRAUD PREVENTION VIDEOS
1. Top 5 Amazon Scams in 2024 2. Top 5 PayPal Scams in 2024 3. How to spot a scam Email in 2024
- Latest Posts by Selma Hrynchuk
-
How To Stop Robocalls
- -
Taking Control of Your Data Privacy: Protecting Yourself in 2024
- -
The Urgency of Removing Personal Information from the Internet
- All Posts














