Types of Cyberattacks and How To Avoid Scams
You may have heard of malware or phishing before. But how about Zero Day Exploit or SQL injection? DNS Tunneling, Denial of Service or Man in the Middle? If you still need to, this is an excellent guide on educating you about the types of attacks you should be aware of. Let me explain.
Companies are becoming more reliant on digital technology. It speeds up processes. It is a money and time-saving solution. But it also makes businesses more vulnerable to cyber-attackers and scams. Over the last few years, the attacks have become more complex.
Scam Detectors Most Trusted Websites in Online Security
- Guard.io (100): Protect your digital world on any device – Guardio stops scams and phishing in their tracks.
- Incogni.com (100): Delete your personal data from the internet and protect against scams and identity theft.
- ExpressVPN (100) Stay secure and anonymous online - Best VPN Out There
Below, there are 7 types and how they work. Plus, of course, I will add at the end how to avoid the scams.
Companies must educate workers on the different types cyber-attacks so they know what to look out for. The most common cyberattacks include:
1. Man in the Middle
MitM attacks interrupt data traveling from one point to another. They may insert themselves into an unsecured server and access sensitive information.
Alternatively, they may install software into a device infected with malware to process private data.
2. Denial of Service Attack
A denial-of-service attack floods a server with traffic to make it inaccessible. It typically occurs on high-profile websites.
Unlike other cyberattacks, the goal is not to steal information. Instead, it aims to slow or disable the site.
3. SQL Injection
Structured query language (SQL) is a computer language for database creation and manipulation. Attackers may use SQL to inject malicious code into a server to force it to reveal information that is typically protected.
The process can be as easy as entering malicious code into a vulnerable website search box.
Watch the video below to see the SQL injection explained:
4. Zero Day Exploit
Zero-day exploit occurs when the attacker detects network vulnerability before the vendors do. Since vendors are unaware of vulnerabilities, they have not installed a patch to protect their systems. The status increases attack risk.
Cyber-attackers will take advantage of the system’s vulnerable state to steal data or cause damage.
5. DNS Tunneling
The Domain Name System (DNS) connects web browsers to websites. DNS tunneling uses the protocol to send malicious traffic through the system. It allows the attacker to take over the server and infiltrate data.
The last two are the ones you are the most familiar with already, but here they are:
6. Malware
Malware is an abbreviated term for malicious software. It can infect your computer when someone clicks a suspicious link or installs unsafe software. Examples include viruses, worms, and ransomware.
Once malware infects your system, it can block access to the network or components of the network, install additional malware into your system, obtain secure information, or make the system unusable.
7. Phishing
Phishing involves sending fraudulent communication disguised as a reputable source. It usually comes through email. For example, you may get a phishing email that looks like it comes from a partner company. But when you look closely, you will see that the spelling of the recipient email is off.
Phishing scams will typically have a link that you can click on. If you click on the link, it’s likely to install malware into your computer that will steal sensitive information.
How to Protect Yourself Against Cyberattacks and Scams
Here are 11 effective measures to stay away from fraud:
1. Activate Multifactor Authentication
Also known as two-factor authentication, MFA will ask you to take an extra step before you log into websites. Most will send a code to your email or cell phone that you must enter along with a passcode before accessing a site. It makes it difficult for anyone other than authorized personnel to gain access.
2. Update Your Software
Networks are constantly updating to offer better protection against cyberattacks. But the protection will only activate if you update your software. An update will eliminate bad actors. Use automatic updates to ensure you have the latest version of the software.
3. Beware of Suspicious Links
Phishing attackers will mimic the appearance of emails that come from trusted sources. But if you look closely, you will see that they are a little off. Examine communication closely before clicking on links.
4. Use Strong Passwords
Avoid using predictable passwords like “password” or “12345678”. Use long passwords with a combination of letters, numbers, and characters. Make unique passwords for various sites. A password randomly generated by a computer typically offers better protection than one created by a human.
5. Watch Out for Suspicious Activity
Beware of suspicious activity that asks you for personal information or offers something too good to be true. Refrain from clicking links that don’t come from reliable sources.
6. Use Biometric Scans When Possible
Devices that use fingerprints and facial recognition offer superior protection.
7. Be Careful When Sharing Personal Information
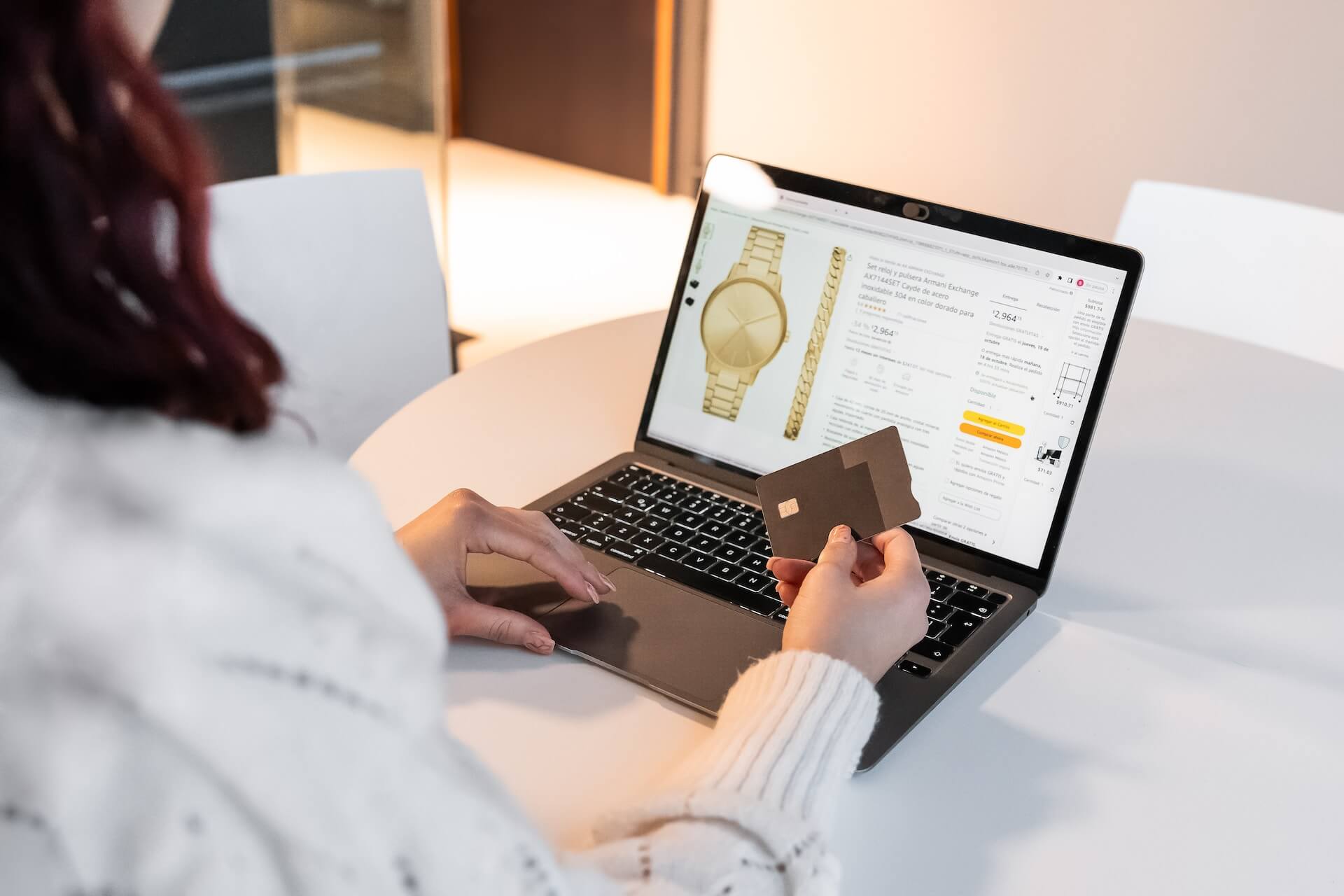
Only share personal information like bank account numbers, credit card numbers, and social security numbers on secure networks that start with https://. Consider using Virtual Private Networks that provide increased security when sharing sensitive data.
8. Use Protective Software
Protective software like antivirus, anti-malware, and firewalls will help keep your systems safe from cyberattacks.
9. Back-Up Files
Use file encryption to back up files. This solution will translate data into a code only decipherable to approved parties.
10. Beware of Scams
Be aware of scammers that pose as government agencies asking for money or personal information. Legitimate organizations will never call, text, or try to contact you through social media.
Scammers may also contact you, offering work-at-home opportunities, debt consolidation, or debt repayment plans. Research to ensure you are working with a legitimate agency before providing any sensitive data.
11. Take Action During a Cyber Attack
If you suspect a cyber attack has occurred:
- Check your financial statements for suspicious or unrecognizable activity
- Change your passwords immediately
- Consider turning off the device and taking it to a professional who can scan it for viruses
- Let involved parties know about the attack
- Run a security scan on the system to check for viruses
- If you detect illicit activity, disconnect the device and perform a complete restoration.
How To Report Cyber Attacks
After a cyberattack occurs, reach out to your financial institutions so they can monitor your accounts. You may have to place holds on accounts with suspicious activity.
You may also file reports with:
The Office of the Inspector General
The FBI Internet Crime Complaint Center
The local police
The Federal Trade Commission
Increased reliance on digital platforms results in additional cybersecurity risks. Familiarize yourself with various types of cyberattacks and scams. Take the proper measures to keep your company protected. The tips in this article will get you headed in the right direction.

TOP MUST-WATCH FRAUD PREVENTION VIDEOS
1. Top 5 Amazon Scams in 2024 2. Top 5 PayPal Scams in 2024 3. How to spot a scam Email in 2024
- Latest Posts by Justin Guttierrez
-
WhatsApp Scammer List
- -
5 Most Common Zoom Scams and How To Avoid Them
- -
How to Use Proxy Chains to Protect Your Identity
- All Posts














